Service Exposure
Table of contents
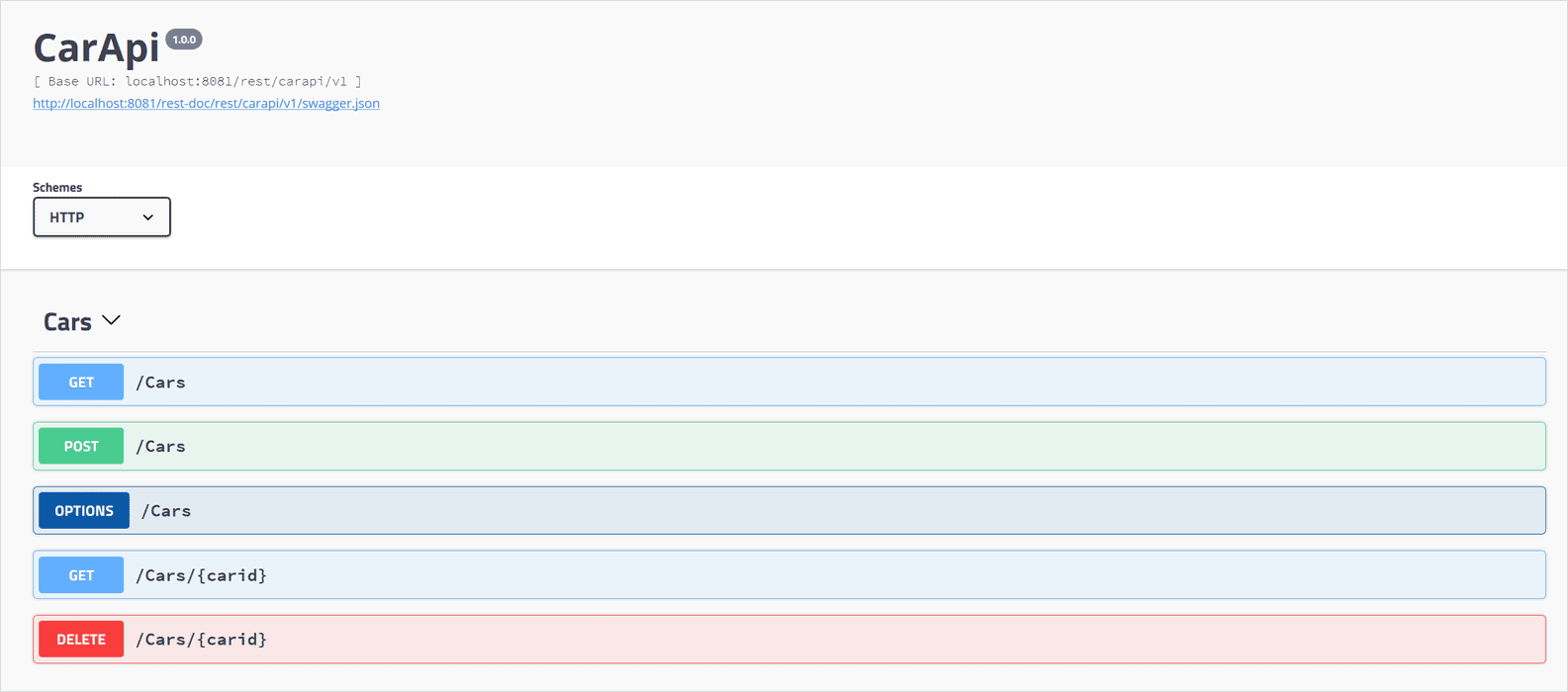
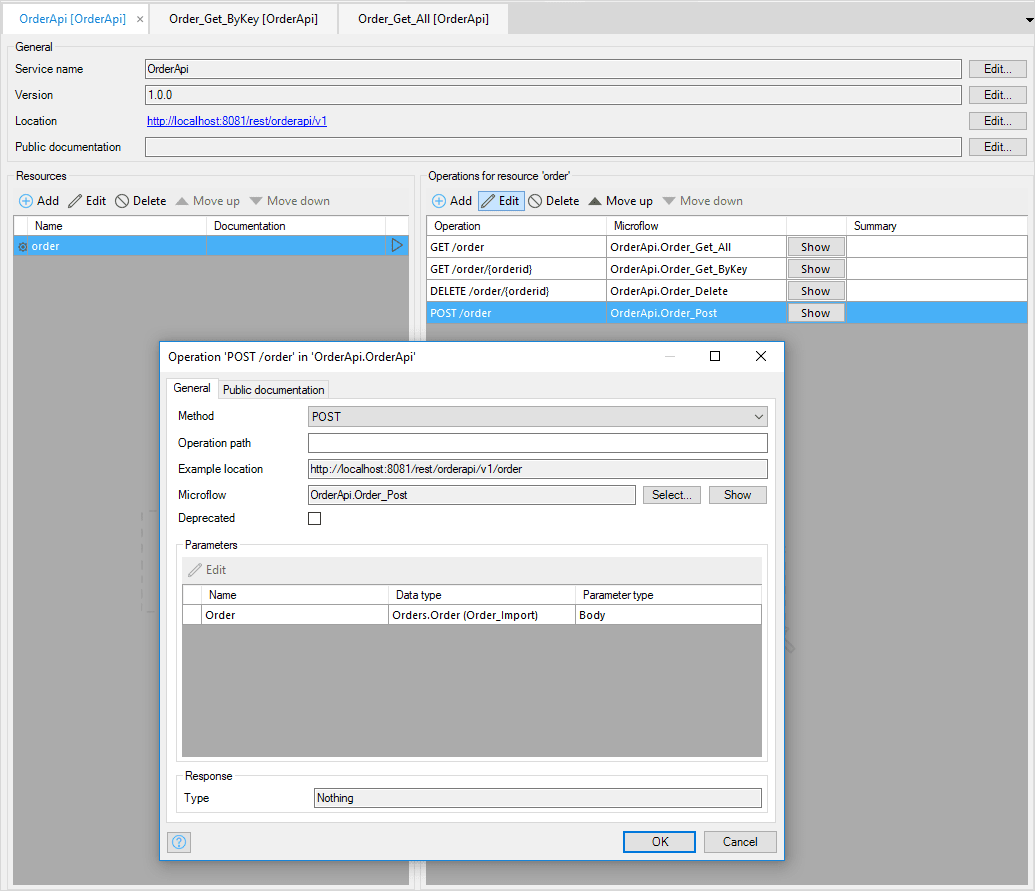
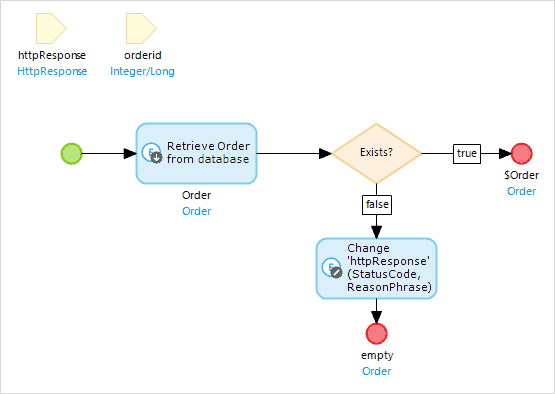
How Can I Publish a REST API?
Whether you want full control of the API you implement or you just want to generate a back-end for your mobile application in a few minutes, Mendix can do it.
How Can I Publish a SOAP Service or Web Service?
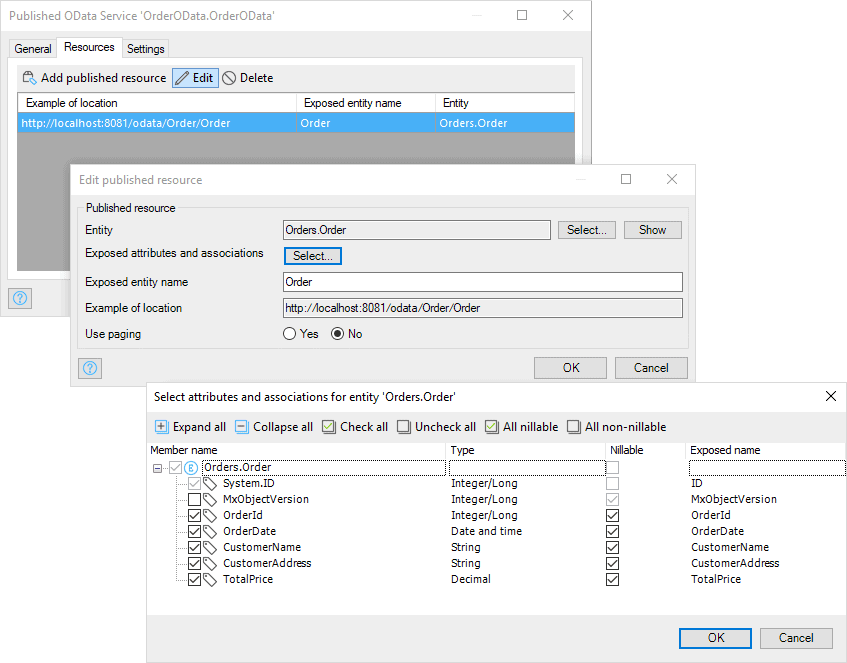
How Can I Publish an OData Service?
How Can I Implement a Custom HTTP Protocol in Mendix?
How Does Mendix Support Swagger and OpenAPI?